There is a systematic order (layer ordering) in networks for data transfer to occur. These layers are responsible for transmitting the data to the other party.
Each layer has a task assigned to it so that it becomes easier to solve the transmission errors of the data and develop the network again.
There are two models in computer networks: OSI Reference Model and IP/TCP Model. (Read the previous article for getting knowledge, you can start from here).
What is OSI Model?
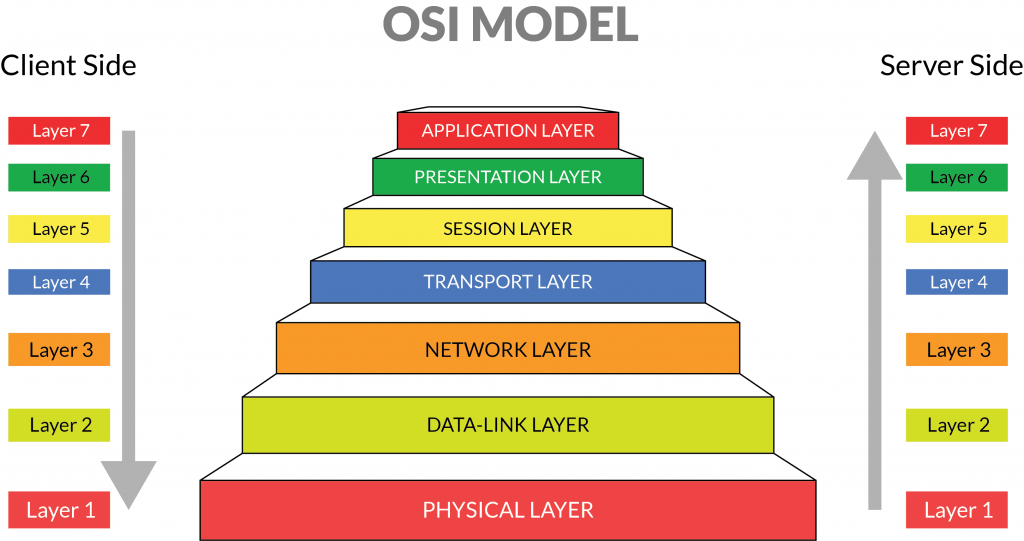
OSI (Open System Interconnection) model was developed by ISO. This model defines how data is moved between devices connected to the network.
As the data passes through the OSI layers, it takes on new tasks. After the 7 layers, the data to be sent is transmitted to the other party.
Data has to pass through each layer (cannot be missing). If any layer is skipped, the data will not reach the other party incomplete or not at all.
Physical Layer
The lowest layer of the OSI model (the layer where the first connection is established) is the physical layer.
It is responsible for the physical connection. The physical layer contains bits of data, it transmits bytes one by one from one node to another.
This layer converts the received data to 0 and 1 format and sends it to the Data Link layer, which reassembles the data.
The physical layer provides bit synchronization. The physical layer controls the sender and receiver according to the clock so that the bit level is synchronized.
The physical layer controls the bit rate and defines the transmission rate. The physical layer also defines the topology (star, bus).
The physical layer defines how data is transferred between two connected devices. There are 3 types of transmission modes (Simplex, half-duplex, and full-duplex).
Data Link Layer
The task of Layer 2 is to make a complete and reliable transfer in the environment. Bit-type data is converted into stream blocks and frames for complete sending here.
In addition, the data link layer identifies other computers on the network and determines who is currently using the cable.
1 frame is created by adding a flag, header (at the end of the first flag), and trailer (at the end of the first flag) to the sender’s data (in bits), beginning and end.
Error Handling: Responsible for editing missing, duplicated, damaged frames. Thus, faulty or damaged frames do not reach the receiver.
Flow Control: It prevents a fast transmitter from damaging the slow receiver. This is a useful feature in all situations, voluntary and involuntary.
Network Layer
The network layer finds the best way to send the packets and directs the packets there. (the physical network where it can send data freely and quickly).
Frames are split here and sent in packets (a small segment of a larger message) over the network, then reassembled at the receiving end.
When the data is to be received, the data in the Data Link Layer is accepted. data is divided into parts, encapsulated, and sent to the transport layer.
The network layer provides congestion control when subnets are overloaded by packets. In this way, congestion can be controlled.
The main task of the network layer is to route packets from the host to the destination host.
Transport Layer
This layer ensures complete and reliable delivery of packet data packets. It also has functions such as error control and flow control.
It is the layer that provides a logical connection between the network and application layers. It combines the segments in the network layer and gives it to the upper layer.
The transport layer adds the destination and source port numbers to the packets. It allows one IP address to handle multiple jobs by dividing IP addresses into ports.
Session Layer
The session layer is responsible for establishing the connection and maintaining the sessions.
The layer allows two processes to establish a connection, and the session layer also has the link termination authority.
In short, this layer prepares and terminates sessions to send data to the right device, since a device is in communication with more than one device.
Presentation Layer
The presentation layer works to prepare, organize and encrypt the data from the session for application.
The resulting data is now formatted in a way that the receiver can understand (translations like ASCII are done).
If necessary, this data can be encrypted. Thus, it cannot be read even if the data is stolen while passing through the season.
Application Layer
This layer controls the input and output of data and provides application functions. The Application layer allows the user to access and manage files on the device.
The ability to access information from websites is an example of the application layer. Users access all network services and applications at this level.
Many features such as sending mail, downloading and storing files, and communicating with the website are realized through this layer.