Search engines are filled with more and more data and information every day. Search engines are your best friend when you want to gather information.
This article has been prepared to show you how to find the information you are looking for in search engines and how this process works.
What is Google Dorking?
Basically, Google Dorking is trying to find necessary (or random) information about a target by limiting the search query.
Various useful information such as which technologies the target is using and key data required for social engineering can be obtained by this method.
Is Google Dorking Legal?
One of the first questions that come to mind is whether this business is legal. There is nothing technically illegal (but not 100% legal).
There are some exceptions, for example collecting information is a passive process, unless you use them you are not considered to have engaged in any illegal business (which may vary in some cases).
For example, if you found a PDF file on Google, saving it to your computer may cause you problems. Or trying passwords you find on a page can also cause problems.
Although what you’re doing is usually legal, it’s important to be careful if you think you’ve crossed the line, back off cautiously.
Google Operators For Advanced Searching
There are some operators at Google to focus search queries on a specific target and topic (to push unnecessary information out of the field).
1 – site operator
The site: operator is used to aggregate the search query into a known site. It is added after the query.
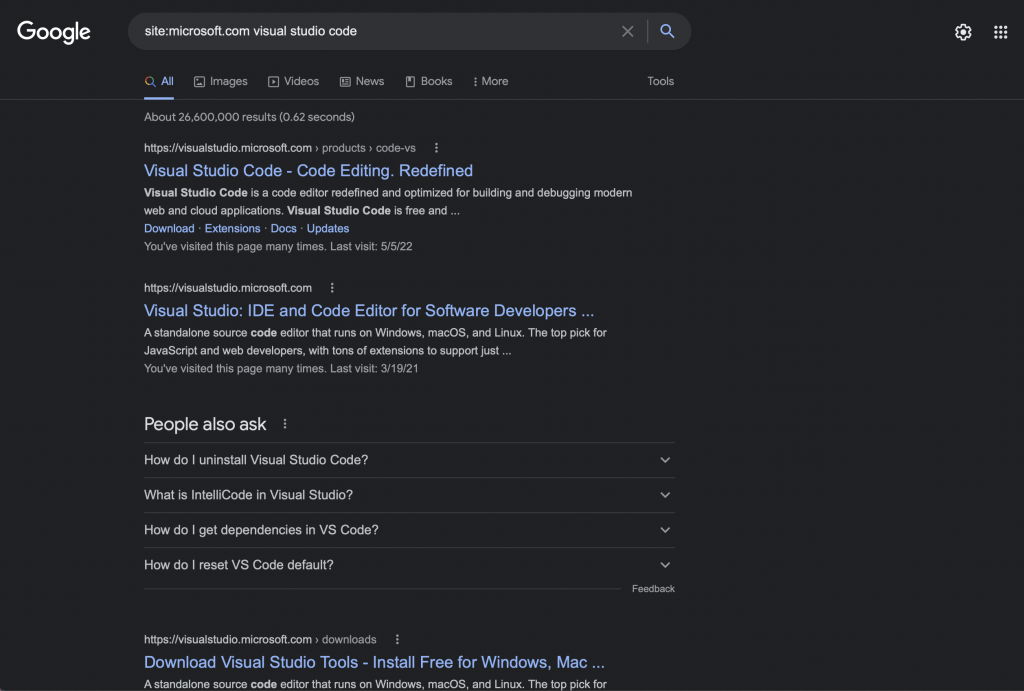
The site operator has limited my search query to Microsoft website and its subdomains only so that I can take information from 1 source.
If the keywords next to the site operator are on the site (not necessarily found in the title), they will be listed.
2 – filetype operator
It searches the query you provide on the search engine like a file. When you type filetype:pdf, the query is searched as a pdf file.
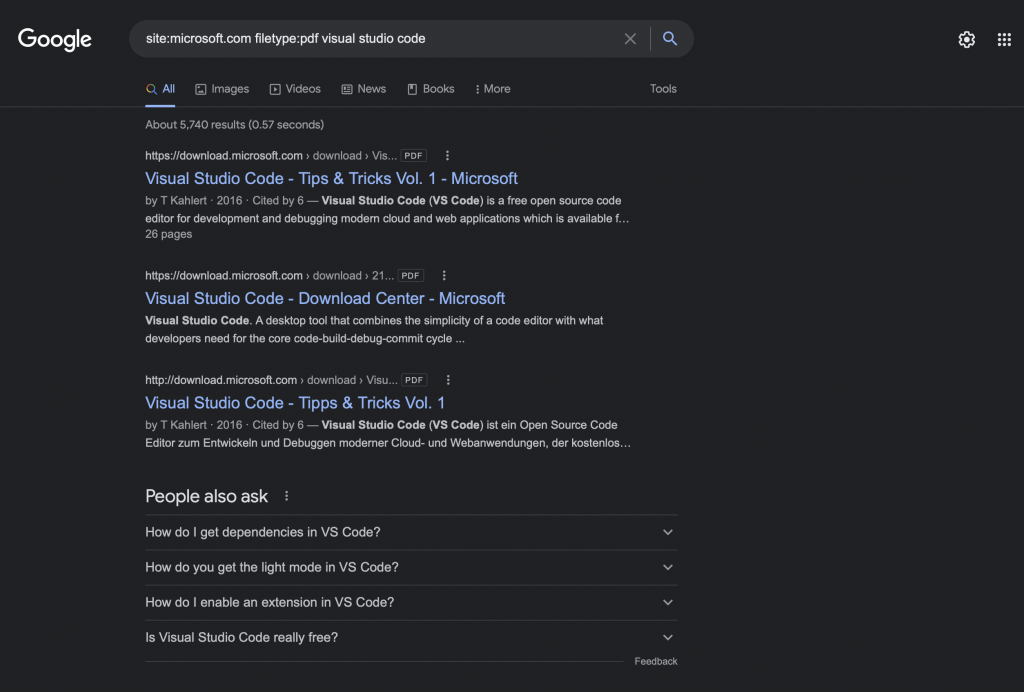
The domain of your search query has started to decrease. Now, pdf files containing visual studio code keywords on microsoft.com are being searched.
Remember that each word with a space is a separate keyword, for example, visual studio code represents 3 separate keywords, these are code, visual, and studio.
3 – intitle operator
With the help of this operator, you can request pages with a title with the string you specify.
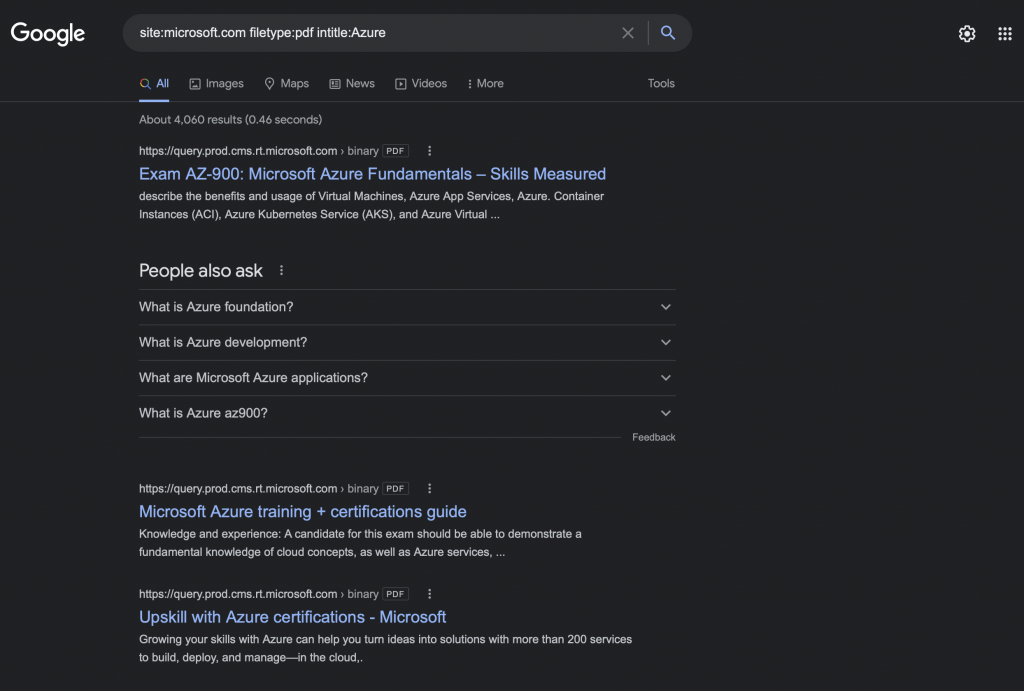
We got rid of the keywords here and now we only see files that contain the Azure text in the title.
Since there is no keyword next to the intitle operator, even if the file contains Azure, it is not listed if there is no Azure in the title.
4 – inurl operator
This operator is used to search on the URL, for example, it can be used to examine the website URL parameter.
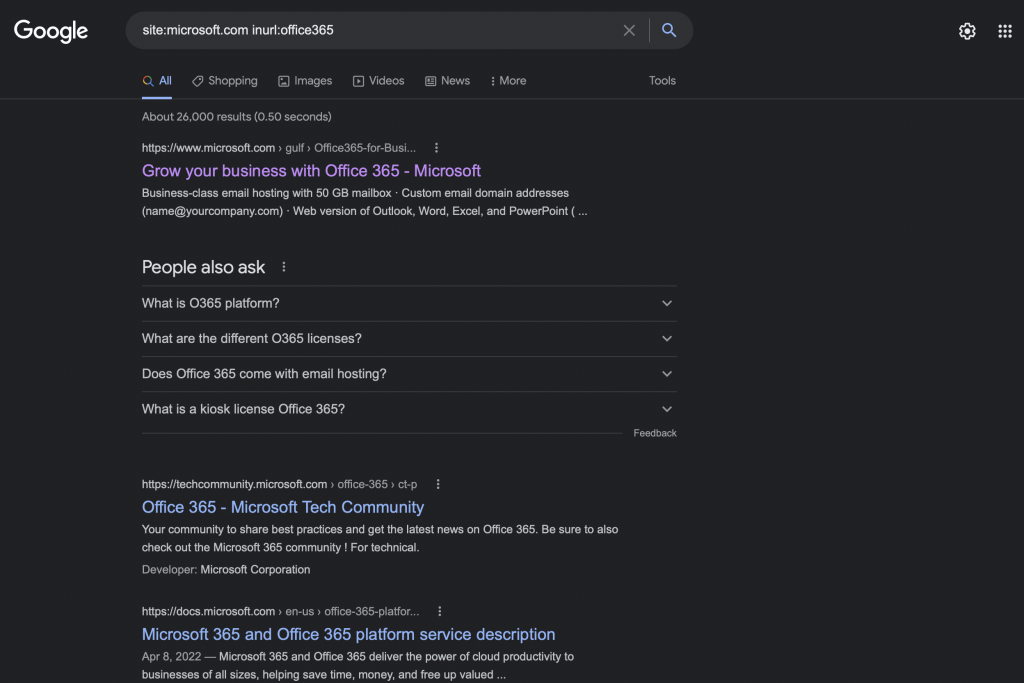
Here, the inurl operator filters URLs that do not contain office365 parameters and thus helps you reach the resource you want.
Using Google Hacking Database
You can use Google Hacking Database for search queries. This database offers google queries to gather useful information.
For instance, we need some pdf documents about our target and we don’t know how to get them. We can find queries about this in GHDB.
The website template looks like this, pretty simple. All queries are listed in this section, we have a query search bar at the left-top.
Now, let’s search query for getting pdf files from the target website. Since this query is a basic query, the results will be similar.
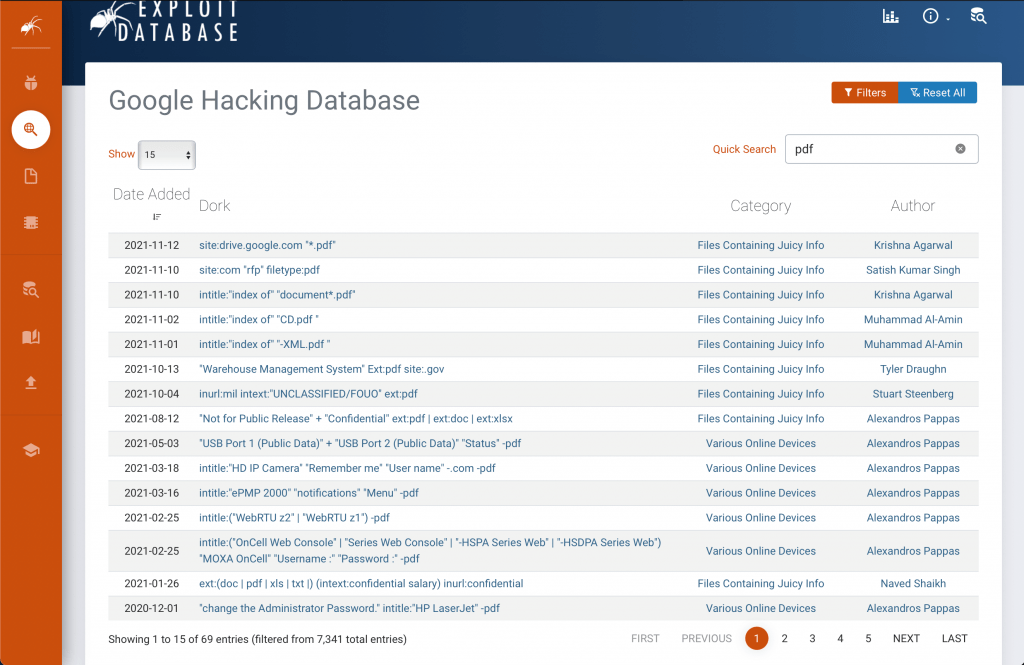
You can get more information by clicking on the dork. Dork offers the author’s name, added date, etc.
Of course, this database just is not searching for basic queries. This database lists complex google queries that allow you to access sensitive information.
Conclusion
We are going to learn how to use Google for gathering information. The solutions here are all manual solutions.
With the help of tools such as TheHarvester and DataSploit, you can complete your work one click faster.
Although automation has made collecting information easier, it is important to always perform manual searching.
